Security Technical Architecture
Identity Server
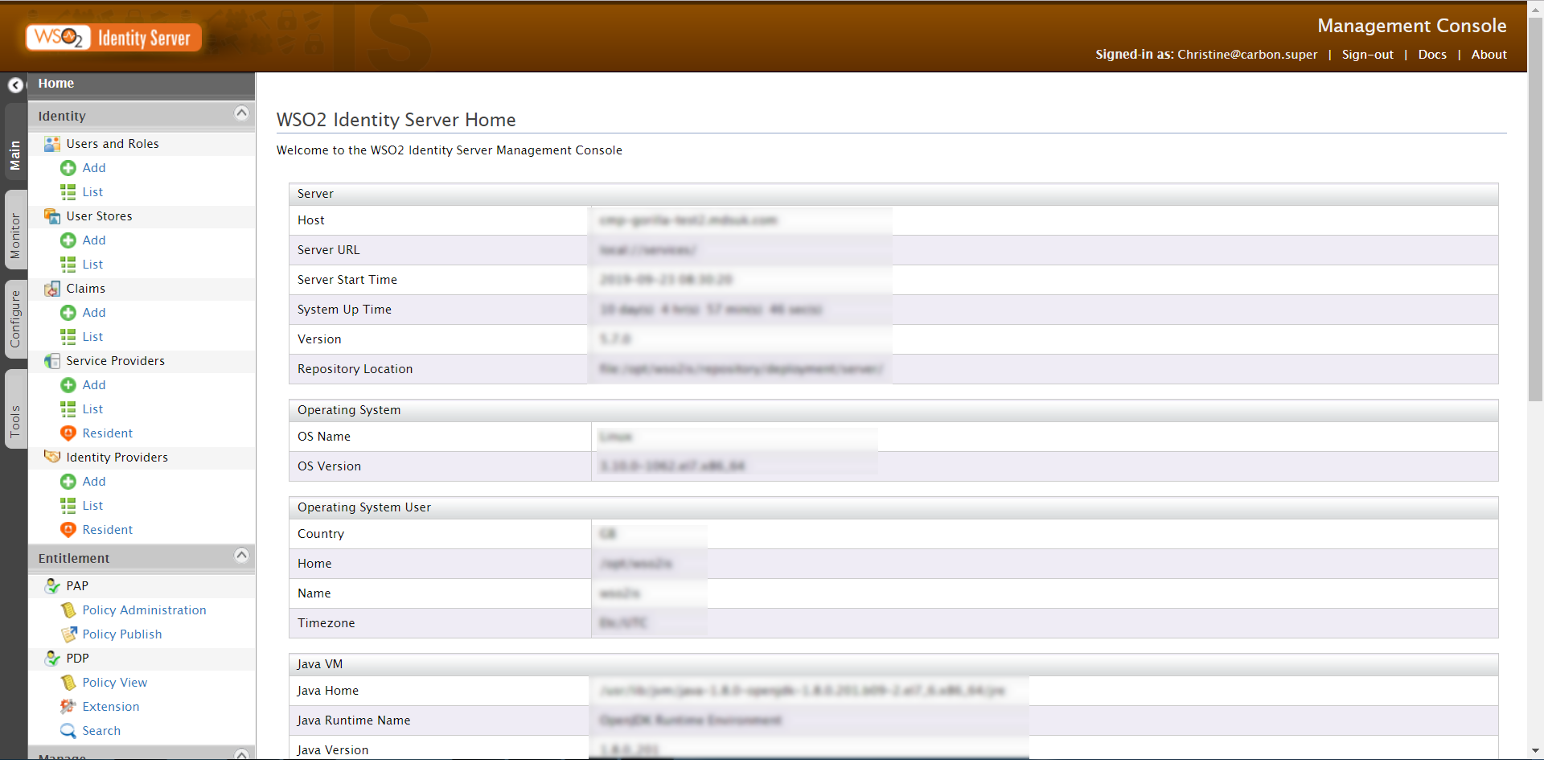
CMP![]() Converged Monetisation Platform. The MDS Global product that supports customer care and billing for digital service providers. is built to use industry standard OAuth2 for authorisation. The WSO2 Identity Server is deployed as part of CMP to provide the Identity and Access Management.
Converged Monetisation Platform. The MDS Global product that supports customer care and billing for digital service providers. is built to use industry standard OAuth2 for authorisation. The WSO2 Identity Server is deployed as part of CMP to provide the Identity and Access Management.
Identity Server Interface
In a standalone CMP installation, users and roles can be maintained directly in the Identity Server however, it can also be configured to use an external identity provider.
You can also create users in the Administration Console![]() An operations web console that allows batch jobs to be scheduled, run manually and monitored. The console also provides for viewing and modification of business and user applicable system configuration..
An operations web console that allows batch jobs to be scheduled, run manually and monitored. The console also provides for viewing and modification of business and user applicable system configuration..
For information on installing and configuring the Identity Server, see the CMP Installation Guide.
Administration Console
You can create users and assign them access to CMP applications and functionality in the Administration Console. See the Users screen and the online help for more information. More granular maintenance, for example assigning roles and permissions, takes place directly in Identity Server.
Single Sign-On
CMP security architecture supports single sign-on when all applications are registered with the Identity Server in the same domain.
Role Extender
The authorisation implementation in many parts of CMP uses very granular level roles for maximum flexibility and future proofing. It would be too cumbersome to have to grant access to all of these granular roles directly to users. A number of granular roles are therefore mapped to higher level business roles and access is granted to these business roles.
For more information, see Security Groups.
The Role Extender takes a role to which access has been granted in the Identity Server and returns the full list of lower level roles that this maps to. CMP components use roles to which that access has been directly granted and the corresponding extended lists of roles returned by the Role Extender to determine whether to allow an action to be performed.
The mapping of business roles to granular roles is factory configuration that is not designed to be modified when CMP is installed.